Why Us
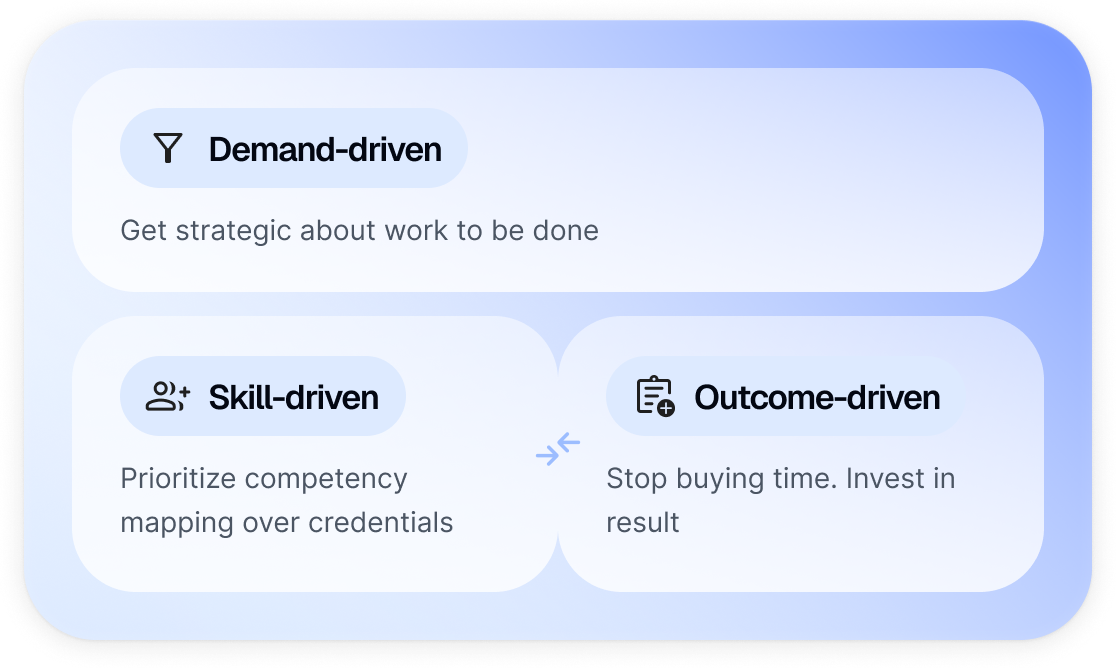
The new operating system to buy talent
Driving the convergence of contingent labor and services (SOWs) into a single, fully integrated talent ecosystem. Breaking down silos. Creating efficient pathways to access all external workforce capabilities from staff augmentation to outcome-based partnerships. Software so intuitive your people will actually use – and love it.